I remember the first time I truly grasped the scale of modern digital encryption. It was during a cybersecurity workshop, and the instructor explained that breaking a standard 256-bit encryption key using a classical supercomputer would take longer than the age of the universe. I recall feeling a sense of immense security, a quiet confidence that our digital world, from banking to personal messages, was fundamentally safe. But then, the conversation shifted to quantum computing, and that sense of security began to waver.
The idea that a revolutionary form of computation could dismantle the very foundations of our digital defenses isn't just a sci-fi plot; it's a very real, very pressing concern for governments, corporations, and everyday users worldwide. Quantum computers, operating on principles that defy our everyday intuition, promise to solve problems currently intractable for even the most powerful supercomputers. But this unprecedented power comes with a potentially destructive side effect: the ability to crack most of the encryption methods that secure our internet today.
This isn't just about faster calculations; it's about a fundamentally different way of processing information. If you've ever wondered if your online passwords, financial transactions, or even national secrets are truly safe in the long run, then you've stumbled upon one of the most significant technological challenges of our era.
## The Unseen Strength: How Classical Encryption Works
Before we dive into the quantum threat, it’s crucial to understand what makes our current encryption so robust. Most of the security underpinning our digital lives, especially for sensitive data, relies on what's known as **public-key cryptography**. The most famous example is RSA (Rivest-Shamir-Adleman), which secures everything from secure websites (HTTPS) to email and virtual private networks (VPNs).
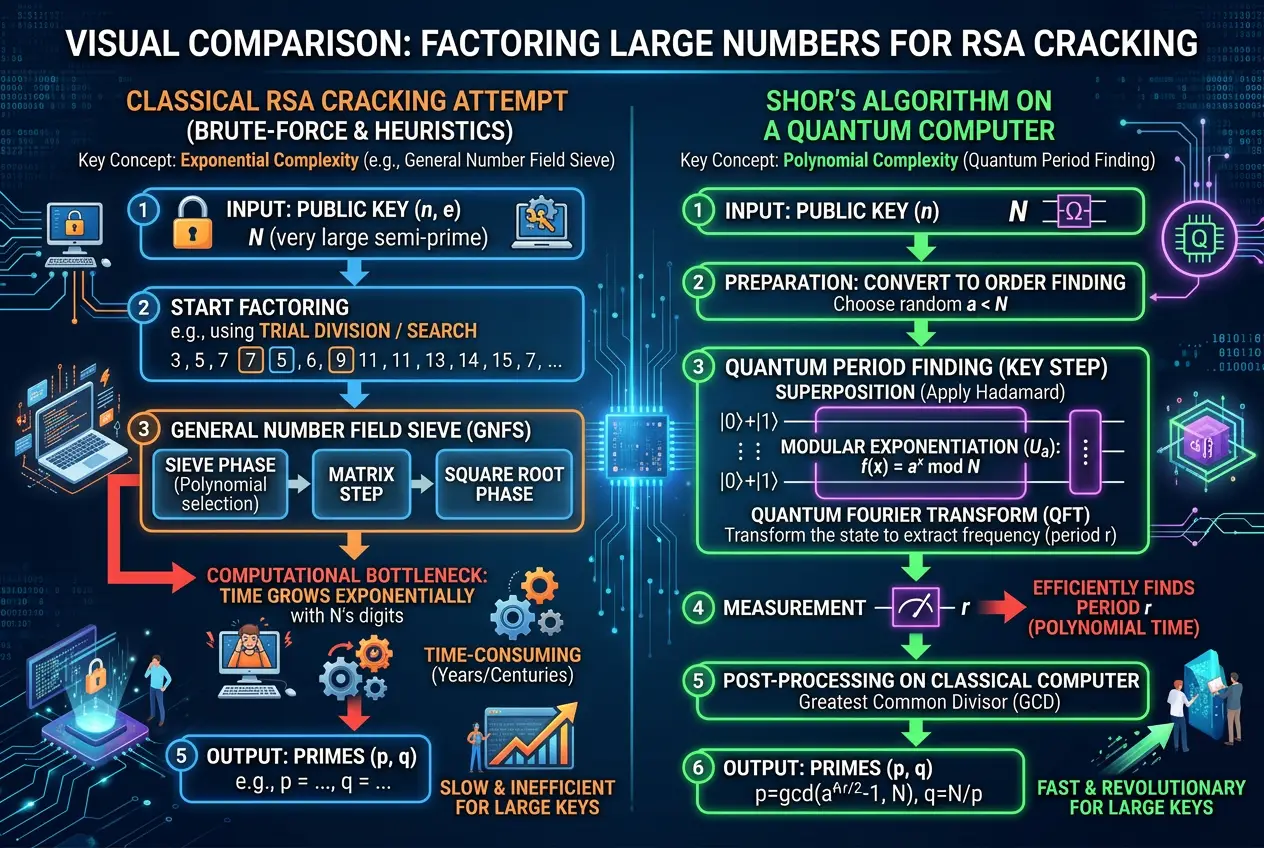
The strength of RSA, and similar algorithms, lies in the difficulty of factoring large numbers. Imagine two very large prime numbers multiplied together to get an even larger composite number. It's easy to multiply them, but incredibly difficult to reverse the process – to find the original two prime factors given only the composite number. This mathematical asymmetry forms the backbone of RSA: your public key is the composite number, which anyone can use to encrypt a message for you, but only you, with knowledge of the two prime factors (your private key), can decrypt it. Without the private key, an attacker would have to try factoring that massive number, a computational feat that, as mentioned, would take an astronomical amount of time with current technology. You can read more about its intricate mathematical details on [Wikipedia's RSA page](https://en.wikipedia.org/wiki/RSA_(cryptosystem)).
## Enter the Quantum Realm: A New Kind of Computation
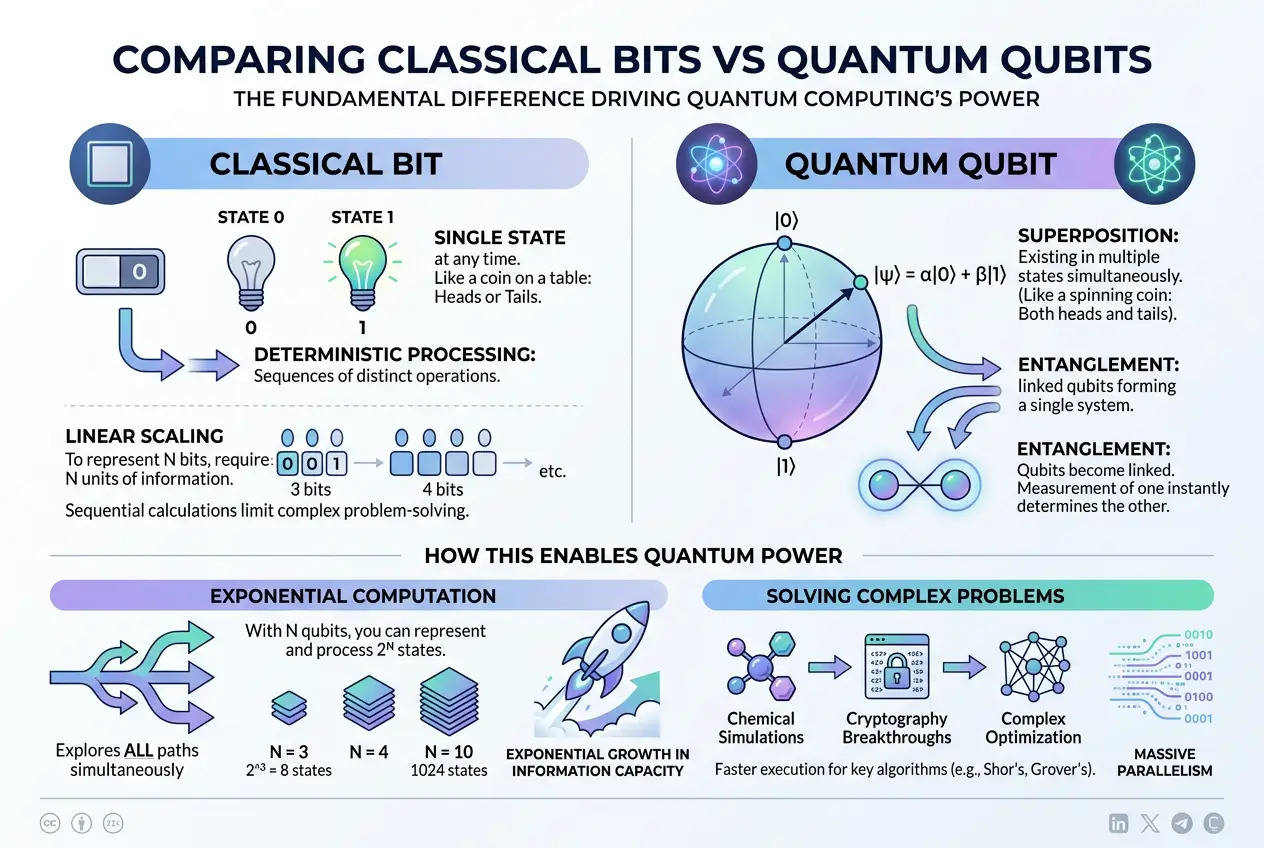
Quantum computing isn't just a faster version of traditional computing; it's a paradigm shift. While classical computers use bits that are either 0 or 1, quantum computers use **qubits**. Qubits can exist in a superposition, meaning they can be both 0 and 1 simultaneously. Furthermore, multiple qubits can become **entangled**, where the state of one instantly influences the state of another, regardless of distance. This allows quantum computers to perform computations on many possibilities at once, a phenomenon known as quantum parallelism.
This ability to explore a vast number of possibilities concurrently gives quantum computers their unprecedented potential. Where a classical computer would have to check each potential factor for a large number one by one, a quantum computer can explore many factors simultaneously. This fundamental difference is what makes them a potential game-changer, not just for encryption, but for fields like material science, drug discovery, and artificial intelligence. The very nature of this computational power is what makes the prospect of a world where light could replace silicon in future computers so exciting, a concept explored in previous discussions on our blog at [Could Light Replace Silicon in Future Computers?](/blogs/could-light-replace-silicon-in-future-computers-6600).
"The good thing about quantum mechanics is that it's difficult to understand, so you don't have to worry about all your data being immediately compromised. But the bad thing is, it's not impossible." – *Adapted from a quote by Scott Aaronson, a prominent quantum computing theorist.*
### Shor's Algorithm: The Encryption Killer
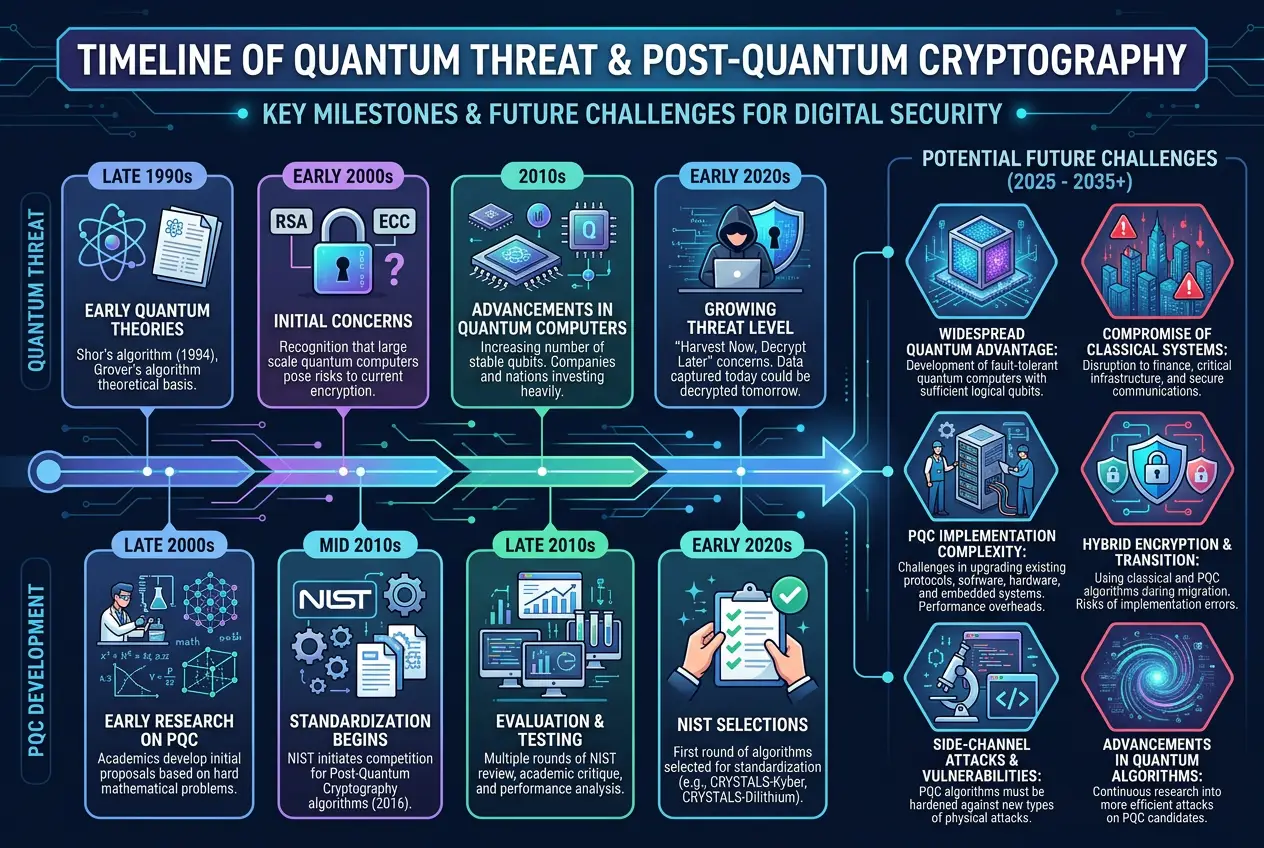
The most direct threat to current encryption comes from **Shor's algorithm**. Developed by Peter Shor in 1994, this algorithm demonstrates that a sufficiently powerful quantum computer could factor large numbers exponentially faster than any classical computer. For context, an encryption key that would take a classical supercomputer billions of years to crack could theoretically be broken by a quantum computer running Shor's algorithm in a matter of hours or days, once quantum computers reach a certain scale and stability.
This is not a hypothetical "what if." Shor's algorithm is a proven mathematical fact. The only reason it hasn't decimated our digital security already is that building a quantum computer capable of running it on large enough numbers (i.e., those used in real-world encryption) is incredibly challenging. Current quantum computers are still in their infancy, often called "NISQ" (Noisy Intermediate-Scale Quantum) devices, meaning they have limited qubits and are prone to errors. However, the progress is rapid. You can delve into the mathematical elegance of Shor's algorithm on its [Wikipedia page](https://en.wikipedia.org/wiki/Shor%27s_algorithm).
### Grover's Algorithm: Attacking Symmetric Keys
While Shor's algorithm targets public-key cryptography (like RSA and ECC), another quantum algorithm, **Grover's algorithm**, poses a threat to symmetric-key encryption (like AES, used for encrypting data at rest or in transit after a secure connection is established). Grover's algorithm offers a quadratic speedup for searching unsorted databases. In the context of cracking symmetric keys, this means it could halve the effective key length. For example, a 256-bit AES key would effectively become a 128-bit key. While this isn't as devastating as Shor's algorithm, which makes factoring practically instant, it still significantly weakens security and means current symmetric key sizes might need to be doubled to remain secure against quantum attacks. More details can be found on [Wikipedia's Grover's algorithm page](https://en.wikipedia.org/wiki/Grover%27s_algorithm).
## The Quantum Threat: When, Not If
The consensus among cryptographers and quantum physicists is that it's not a question of *if* quantum computers will be able to break current encryption, but *when*. Estimates vary widely, from a decade to several decades, largely depending on the pace of quantum hardware development. However, the "harvest now, decrypt later" scenario is a serious concern. Adversaries could be collecting encrypted data today, storing it, and waiting for quantum computers to become powerful enough to decrypt it in the future. This implies that data with a long shelf life, such as state secrets or intellectual property, is already at risk.
The urgency is driving significant research into **post-quantum cryptography (PQC)**, also known as quantum-resistant cryptography. These are new cryptographic algorithms designed to be secure against both classical and quantum computers. The National Institute of Standards and Technology (NIST) in the U.S. has been leading an international effort to standardize PQC algorithms, with several candidates currently undergoing rigorous testing. These new algorithms are often based on different mathematical problems, such as lattice-based cryptography or code-based cryptography, that are believed to be hard for both classical and quantum computers to solve. For further reading, check out [Wikipedia's Post-quantum Cryptography page](https://en.wikipedia.org/wiki/Post-quantum_cryptography).
## Preparing for the Quantum Leap: Strategies and Challenges
Transitioning to post-quantum cryptography is a massive undertaking. It involves:
* **Inventorying:** Identifying all systems, applications, and protocols that use cryptography. This is far more complex than it sounds, as encryption is embedded everywhere.
* **Upgrading:** Replacing existing cryptographic modules with PQC alternatives. This requires significant software and hardware updates across the entire digital infrastructure.
* **Standardization:** Ensuring that everyone adopts compatible PQC standards to maintain interoperability and prevent new vulnerabilities.
* **Quantum Key Distribution (QKD):** While not a direct replacement for PQC, QKD is a method that uses quantum mechanics to establish cryptographic keys with provable security. It's often seen as a complementary technology, especially for ultra-secure communications channels, though it faces practical limitations in terms of distance and infrastructure.
The scale of this migration is often compared to the Y2K bug, but with potentially far greater implications for security and privacy. Just as AI continues to push the boundaries of what's possible, even questioning if it can truly learn from human intuition as we explored in [Can AI Truly Learn From Human Intuition?](/blogs/can-ai-truly-learn-from-human-intuition-5138), quantum computing challenges our fundamental assumptions about digital security.
## The Horizon: A Quantum-Secure Future?
While the quantum threat is formidable, the future isn't necessarily bleak. The development of post-quantum cryptography is progressing steadily, and experts are working diligently to develop and deploy new algorithms before quantum computers become a widespread threat. Organizations and individuals need to start planning for this transition now, assessing their cryptographic dependencies and preparing for updates.
The irony is that quantum mechanics, which offers the tools to break our current encryption, also offers solutions for truly unbreakable communication through principles like quantum key distribution. It's a testament to the strange and wonderful nature of the universe that the very phenomena that threaten our digital world also hold the keys to its ultimate security. The race is on, not just to build more powerful quantum machines, but to secure our information against them. This reminds me of how we grapple with the fundamental nature of reality itself, even questioning if our reality could be a digital simulation, a fascinating dive found in [Is Our Reality a Digital Simulation?](/blogs/is-our-reality-a-digital-simulation-decoding-the-universes-code-9313).
The quantum revolution is upon us. It promises not just faster computations, but a re-evaluation of our most fundamental digital safeguards. Staying informed and supporting the transition to quantum-resistant technologies will be key to navigating this new era of cybersecurity. The question is no longer *if* quantum computers can break every encryption, but *how quickly* we can build new defenses to ensure they don't.
Frequently Asked Questions
Classical computers rely on bits (0 or 1) and solve encryption problems by trying possibilities sequentially. Quantum computers use qubits (0, 1, or both simultaneously via superposition) and entanglement, allowing them to explore many possibilities concurrently, drastically speeding up certain types of calculations relevant to breaking encryption.
Shor's algorithm is the biggest threat, specifically to public-key cryptography like RSA and ECC. It can factor large numbers exponentially faster than classical computers, which is the mathematical basis for these encryption methods.
Not immediately. Current quantum computers are not yet powerful or stable enough to break real-world, large-scale encryption. However, there is a concept called 'harvest now, decrypt later,' where adversaries could be collecting encrypted data today, intending to decrypt it once quantum computers mature.
Post-quantum cryptography refers to a new class of cryptographic algorithms designed to be secure against attacks from both classical and future quantum computers. These algorithms are based on different mathematical problems that are believed to be hard for quantum computers to solve.
Estimates vary widely, but most experts predict it could be anywhere from 10 to 30 years before quantum computers are powerful enough to pose a significant threat to widely used encryption standards. The timeline depends heavily on breakthroughs in quantum hardware development and error correction.
While individuals don't need to take immediate action, staying informed is crucial. For organizations and developers, preparing involves inventorying existing cryptographic systems, understanding the NIST PQC standardization process, and planning for a gradual migration to post-quantum cryptographic algorithms.
Verified Expert
Alex Rivers
A professional researcher since age twelve, I delve into mysteries and ignite curiosity by presenting an array of compelling possibilities. I will heighten your curiosity, but by the end, you will possess profound knowledge.
Leave a Reply
Comments (0)
No approved comments yet. Be the first to share your thoughts!
Leave a Reply
Comments (0)