I remember as a child, after stumbling upon a documentary discussing the "dark web," a profound question lingered in my mind: *Who owns it?* I imagined a shadowy figure, a digital sovereign ruling over its unseen domains. It felt like something out of a science fiction novel, a clandestine digital empire with a clear hierarchy. But as I delve deeper into the intricate layers of the internet, I’ve realized the reality is far more complex, decentralized, and intriguing than any singular ownership could ever suggest. The dark web isn't a single entity or a company; it's a testament to the internet's anarchic underbelly and its potential for both unparalleled freedom and profound danger.
### The Internet's Hidden Layers: Surface, Deep, and Dark
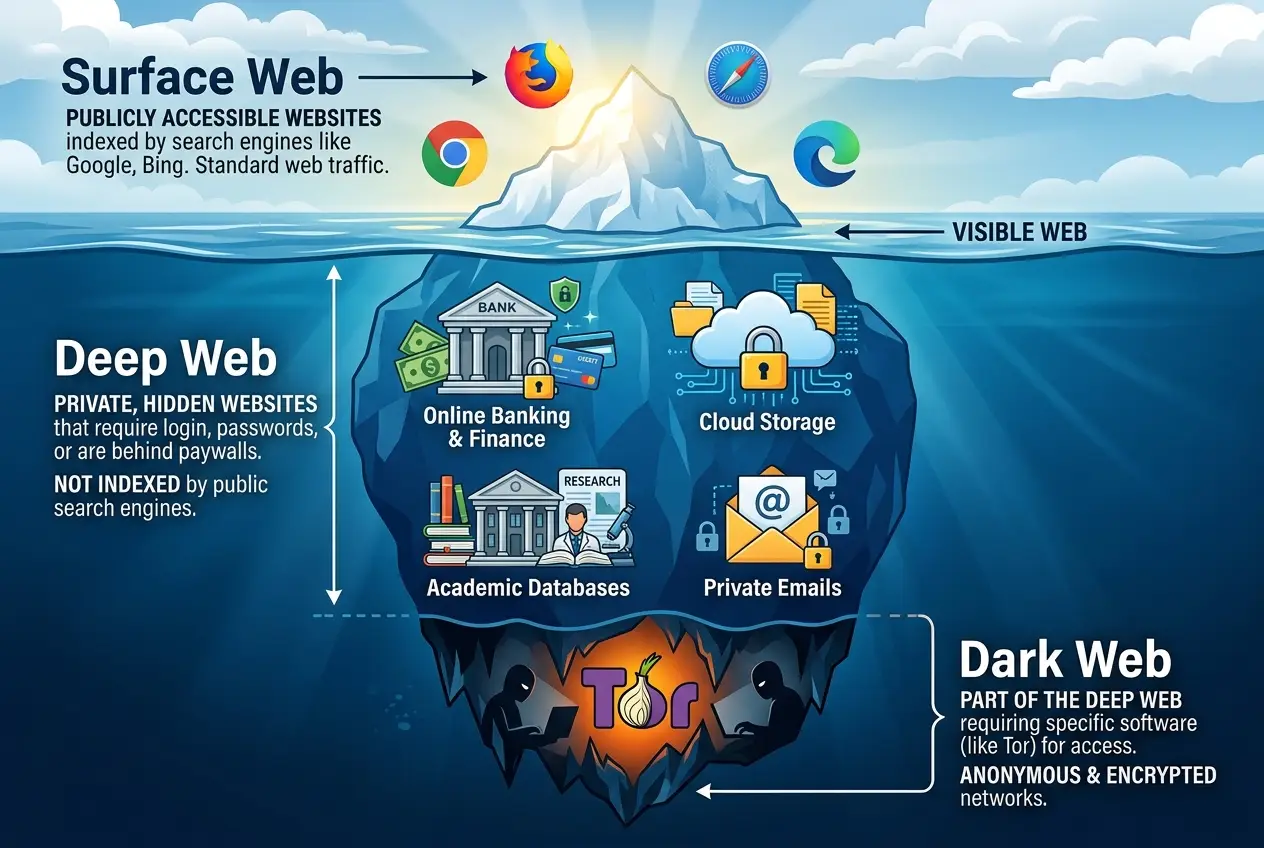
To truly understand the dark web, it's essential to first understand its place within the broader internet landscape. Think of the internet as an ocean.
* **The Surface Web:** This is the part of the internet we interact with daily—websites indexed by search engines like Google, Bing, or DuckDuckGo. It’s the tip of the iceberg, easily accessible, making up only about 4-5% of the entire internet. When I browse my favorite news site or check my social media, I'm swimming in the surface web.
* **The Deep Web:** This massive segment lies beneath the surface. It includes content that isn't indexed by standard search engines, requiring specific login credentials or direct access. Think of your online banking portal, your private cloud storage, or academic databases. It's legitimate, vast, and makes up the vast majority of the internet. We interact with the deep web constantly, often without even realizing it.
* **The Dark Web:** This is a small, specialized portion of the deep web that has been intentionally hidden and requires specific software, configurations, or authorizations to access. It's often associated with anonymity and illicit activities, but it also serves as a haven for privacy advocates, whistleblowers, and those living under oppressive regimes. It’s the deepest, most obscured part of the internet ocean.
### Decoding the Technology: How the Dark Web Operates
The primary gateway to the dark web is **Tor** (The Onion Router). Tor isn't just a browser; it's a network designed to enable anonymous communication. The "onion" in its name refers to the layering of encryption used to protect user identity. When you access the dark web through Tor, your internet traffic is routed through a series of volunteer-operated relays, encrypting it multiple times. Each relay decrypts one "layer" of the onion to reveal the next relay's address, until the final layer is stripped, and the traffic reaches its destination. This multi-layered encryption makes it incredibly difficult to trace the user's IP address or location.
This technology isn't new. Tor's origins trace back to the U.S. Naval Research Laboratory in the mid-1990s, initially developed to protect U.S. intelligence communications online. It was later released to the public for wider adoption, evolving into the decentralized network we know today. This historical context is crucial; the very tools enabling dark web anonymity were forged in the fires of national security concerns, highlighting the dual-use nature of many powerful technologies. You can learn more about its fascinating history on [Wikipedia's Tor Project page](https://en.wikipedia.org/wiki/Tor_(anonymity_network)).
Other darknets exist, such as I2P (Invisible Internet Project) and Freenet, each with their own methods of anonymization, but Tor remains the most prominent and widely used for accessing hidden services. These networks aren't owned by a single entity; they are maintained by global communities of volunteers and open-source developers.
### Who "Owns" the Dark Web? A Decentralized Enigma
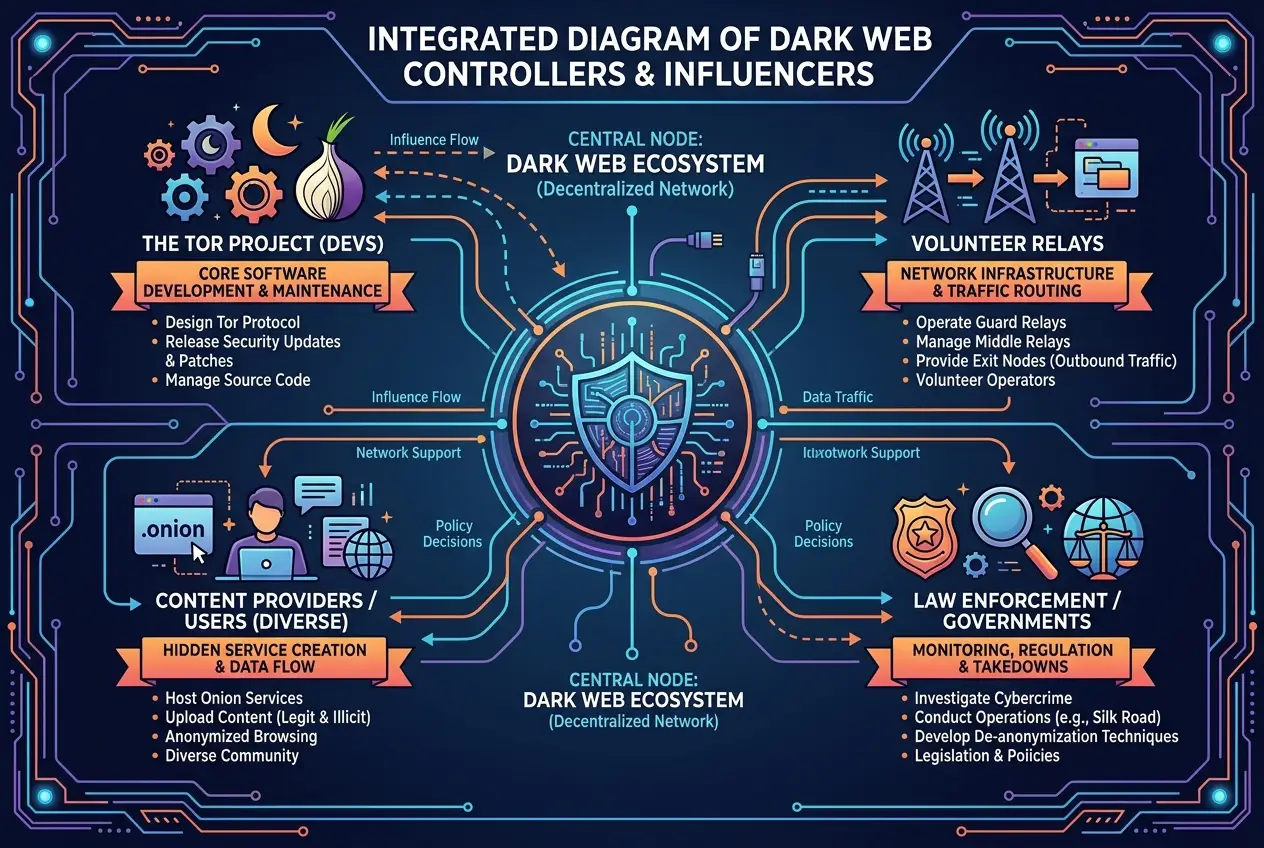
The short answer is: **no one truly owns the dark web.** It operates on a fundamentally decentralized model, which is precisely what gives it its resilience and anonymity. Instead of a single owner, it is a complex ecosystem shaped by various players and forces:
#### 1. The Developers and Maintainers:
The core software that enables the dark web, like the Tor browser and network protocols, is developed and maintained by non-profit organizations and open-source communities. The **Tor Project**, for instance, is a U.S. non-profit organization primarily responsible for maintaining and improving the Tor network. They receive funding from various sources, including government agencies (like the U.S. State Department), grants from foundations, and individual donations. They develop the code, but they don't "own" the network itself or its content. Their mission is to provide privacy and anonymity tools, irrespective of how those tools are used.
#### 2. The Volunteer Network Operators:
The Tor network relies on thousands of volunteer-operated relays around the world. These individuals and organizations dedicate their bandwidth and computing resources to keep the network running, routing traffic for others. Without these volunteers, the Tor network—and by extension, the dark web—would cease to function. These volunteers are not "owners" in a traditional sense, but their collective effort is indispensable.
#### 3. The Content Creators and Users:
The content on the dark web—from legitimate forums and whistleblowing platforms to illicit marketplaces—is created, hosted, and consumed by its users. Anyone with the technical know-how can set up a "hidden service" (a website accessible only through Tor). These users range from journalists in restrictive countries and political dissidents to cybercriminals and hackers. Their activities define the dark web's ever-shifting landscape, making it impossible for any single entity to control or censor all information. This aspect reminds me of the early days of the internet, a wild west of information where communities formed organically. For instance, the discussion around the implications of such decentralized systems for control and governance is always fascinating, much like exploring the concept of the internet gaining a collective mind, as we discussed in our blog, [Is the Internet Gaining a Collective Mind?]( /blogs/is-the-internet-gaining-a-collective-mind-9582).
#### 4. The Governments and Law Enforcement:
While they don't "own" the dark web, governments and law enforcement agencies are significant players in its ecosystem. They actively monitor, infiltrate, and try to dismantle illicit operations. Agencies like the FBI, Europol, and others have had notable successes in taking down major dark web marketplaces and arresting operators. Their presence represents a constant push-and-pull, a cat-and-mouse game between those seeking anonymity and those seeking to enforce the law. This ongoing struggle often brings to mind questions of digital anomalies and unexplained behaviors in computing, as we delved into in our piece, [Digital Anomalies: Can Computers Show Unexplained Behaviors?]( /blogs/digital-anomalies-can-computers-show-unexplained-behaviors-9999).
### Myths vs. Realities of Dark Web Ownership
The myth of a single owner stems from a natural human tendency to seek centralized authority. In reality, the dark web embodies the internet's decentralized spirit.
* **Myth:** A powerful, shadowy cabal runs the entire dark web.
* **Reality:** It’s a distributed network of independent users, developers, and volunteers. No one group has absolute control over its content or infrastructure.
* **Myth:** It's exclusively for illegal activities.
* **Reality:** While it hosts illicit content, it's also used for legitimate purposes like secure communication, journalistic investigations, and anonymous access to information in censored regions. The intent of Tor is privacy, not inherently illegal activity.
This distributed nature means that taking down the "dark web" isn't like shutting down a single server or arresting a CEO. It's more akin to trying to drain an ocean by removing individual drops of water. Even if a major marketplace is shut down, another often quickly emerges to fill the void. This inherent resilience is a core feature of decentralized networks.
### The Power of Decentralization: A Double-Edged Sword
The lack of a central authority is both the dark web's greatest strength and its most significant weakness.
**Strengths:**
* **Resilience:** No single point of failure means it's incredibly difficult to shut down entirely.
* **Anonymity:** Users can communicate and share information with a high degree of privacy, crucial for whistleblowers and activists.
* **Censorship Resistance:** It bypasses state-level internet censorship, offering a lifeline for free speech in oppressive regimes.
**Weaknesses:**
* **Lawlessness:** The anonymity that protects dissidents also shields criminals, making it a breeding ground for cybercrime, drug trafficking, and exploitation.
* **Difficulty in Regulation:** Without central control, regulating content or activity is almost impossible, posing significant challenges for law enforcement.
* **Vulnerability:** Despite its design, users are not entirely immune to sophisticated attacks or de-anonymization efforts by state-level actors.
Understanding this dual nature helps explain why the "ownership" question is so challenging. The dark web is not a product or a service; it's a protocol and an ethos, sustained by a diverse community with varying intentions. The very technologies that allow for this unprecedented level of anonymity also challenge our traditional notions of governance and responsibility. This topic often leads one to ponder the fundamental building blocks of our reality, much like questioning whether tiny strings are the universe's secret code, as explored in our blog, [Are Tiny Strings the Universe's Secret Code?]( /blogs/are-tiny-strings-the-universes-secret-code-1701). The decentralized nature also has parallels with the very structure of the universe, compelling us to ask if the universe itself is a giant neural network, a concept we tackled in depth in [Is the Universe a Giant Neural Network?]( /blogs/is-the-universe-a-giant-neural-network-2907).
### Conclusion: A Digital Frontier Without a Ruler
The notion of a single entity "owning" the dark web is a convenient fiction, a simplification of a far more complex reality. Instead, it exists as a testament to the internet's original promise of a free, open, and decentralized network, pushed to its absolute limits. Its "ownership" is distributed among its developers, its volunteer operators, and the myriad of users who populate its hidden corners.
As technology continues to evolve, the balance between privacy, security, and law enforcement will remain a critical global challenge. The dark web, in all its enigmatic glory, serves as a stark reminder that some digital frontiers may forever remain without a singular ruler, governed instead by the very protocols that enable its existence and the collective actions of its participants. It is a space where the rules of the physical world are bent and often broken, presenting an ongoing mystery that challenges our understanding of control in the digital age.
Frequently Asked Questions
Accessing the dark web itself is not inherently illegal. Many individuals use it for legitimate purposes, such as circumventing censorship, secure communication, or anonymous browsing. However, engaging in illegal activities while on the dark web, like buying illicit goods or participating in cybercrime, is strictly unlawful.
The Tor network, primarily maintained by The Tor Project, is a non-profit organization. It receives funding from various sources, including government grants (like from the U.S. State Department), charitable foundations, private donations, and open-source community support. These funds cover development, maintenance, and operational costs.
No, law enforcement cannot shut down the entire dark web due to its decentralized nature. It's a network of thousands of volunteer-operated relays and hidden services across the globe. While authorities can, and often do, shut down specific illicit marketplaces or servers, new ones typically emerge, making a complete shutdown virtually impossible.
While the Tor network significantly enhances user anonymity by routing traffic through multiple encrypted relays, it does not guarantee absolute anonymity. Highly sophisticated state-level actors or advanced cybercriminals might have the resources to de-anonymize users under specific circumstances, though this is rare for the average user. Best practices for security and anonymity are still crucial.
A hidden service, also known as an onion service, is a website or other service hosted within the Tor network that is only accessible through Tor. Its IP address is hidden, and its location is obscured, providing enhanced anonymity for both the service provider and its users. These services have '.onion' domain names instead of '.com' or '.org'.
Verified Expert
Alex Rivers
A professional researcher since age twelve, I delve into mysteries and ignite curiosity by presenting an array of compelling possibilities. I will heighten your curiosity, but by the end, you will possess profound knowledge.
Leave a Reply
Comments (0)
No approved comments yet. Be the first to share your thoughts!
Leave a Reply
Comments (0)