Imagine a world where your most secure devices—your smartphone, your smart home hub, even industrial sensors—could be compromised not by a malicious line of code or a brute-force attack, but by something far more insidious: **sound**. Not the kind you hear, but frequencies that slip beneath our auditory perception or soar far above it. I’ve been fascinated by the concept of "acoustic hacking" recently, and I have to say, the implications are both astonishing and a little unsettling.
We tend to think of sound as something benign, a medium for music, speech, or the ambient noise of our lives. But sound is energy, a wave of pressure, and like any form of energy, it can be manipulated, directed, and potentially weaponized. Welcome to the invisible frontier of cybersecurity, where infrasound and ultrasound could be the next stealthy tools in a hacker’s arsenal.
The Unheard Spectrum: Infrasound and Ultrasound
To understand how sound could possibly "hack" technology, we first need to appreciate the vast spectrum of acoustic energy that exists beyond human hearing. Our ears are incredibly sensitive, but they only perceive a tiny sliver of reality, typically ranging from about 20 Hertz (Hz) to 20,000 Hz.
* **Infrasound:** These are frequencies *below* 20 Hz, often described as sub-audible or low-frequency sound. Think of the deep rumbles of earthquakes, volcanic eruptions, or distant storms. Elephants and whales use infrasound to communicate over vast distances. While humans can't consciously hear it, prolonged exposure to strong infrasound has been linked to feelings of unease, anxiety, and even nausea. It can resonate with internal organs, leading to strange physical sensations.
* **Ultrasound:** On the other end of the spectrum, ultrasound refers to frequencies *above* 20,000 Hz. Bats and dolphins use ultrasound for echolocation. In medicine, ultrasound imaging is a vital diagnostic tool. In industry, it's used for cleaning, welding, and even non-destructive testing of materials. We can't hear these high frequencies, but they carry significant energy and can be precisely focused.
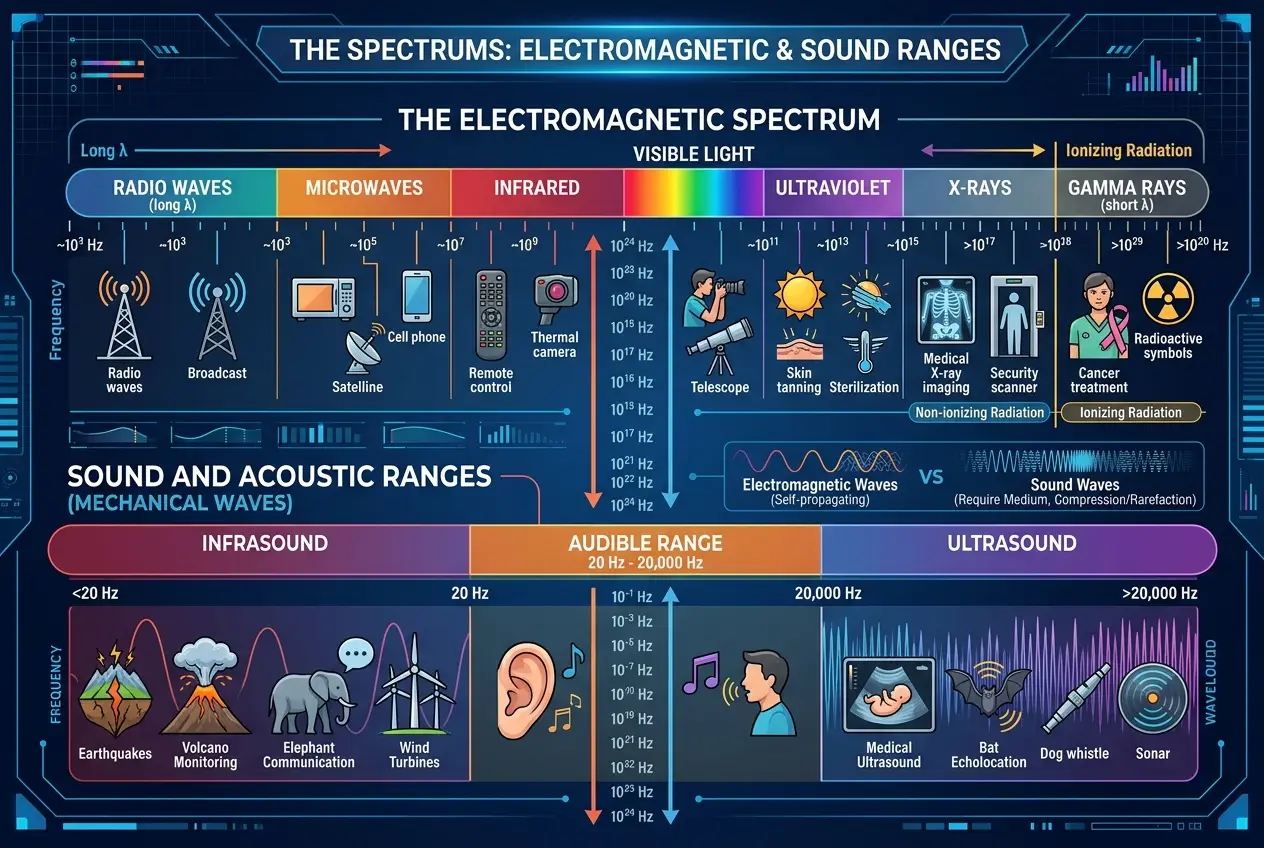
The key insight here is that while *we* might not hear these frequencies, many of our modern electronic devices certainly *can*. Microphones, accelerometers, gyroscopes, and even some internal components are designed to detect vibrations across a broad frequency range. And where there's a sensor, there's a potential vulnerability.
Acoustic Attacks: More Than Just Noise
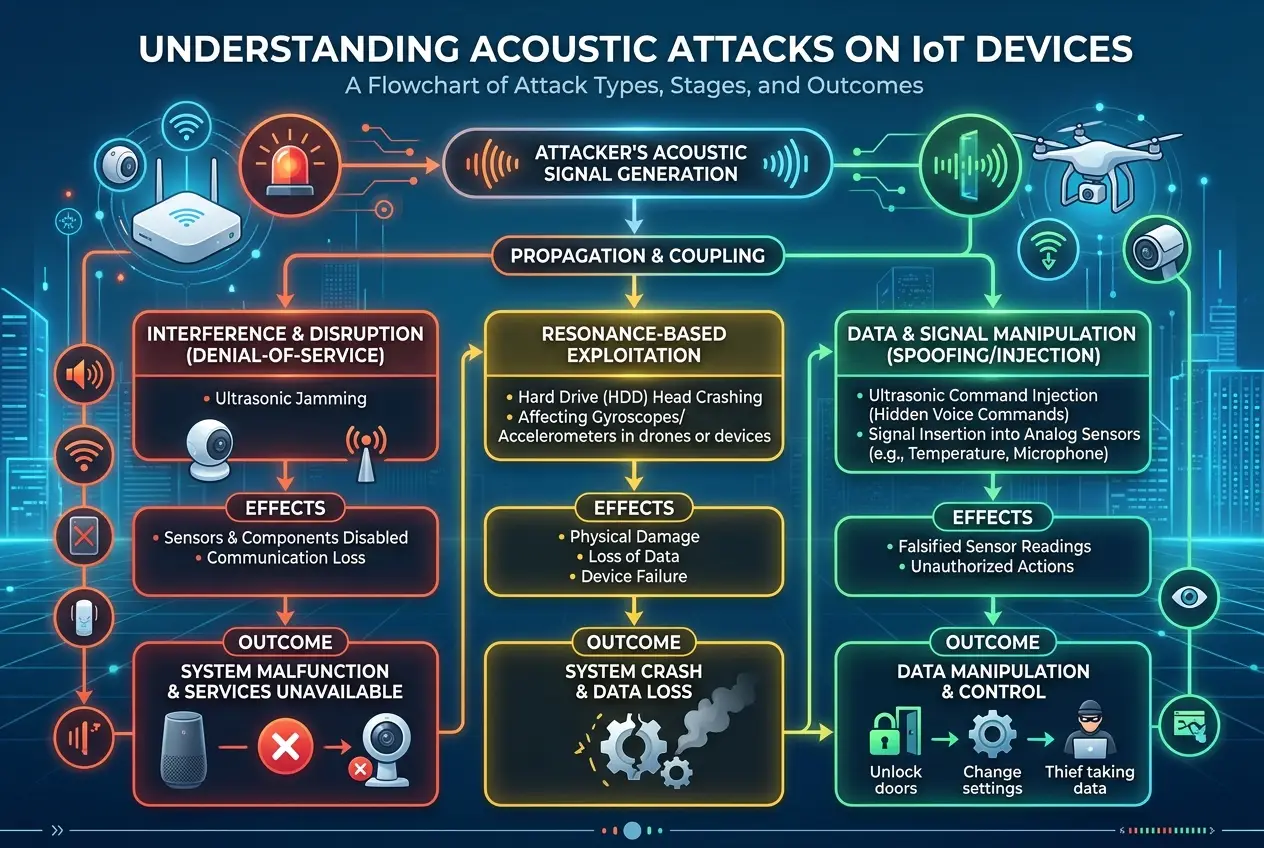
The idea of using sound to influence technology isn't entirely new. Researchers have been exploring this concept for years, but the sophistication and potential impact are rapidly escalating. Think of it not as simply "breaking" a device, but as **manipulating its perception of reality**.
Vibration-Based Exploits
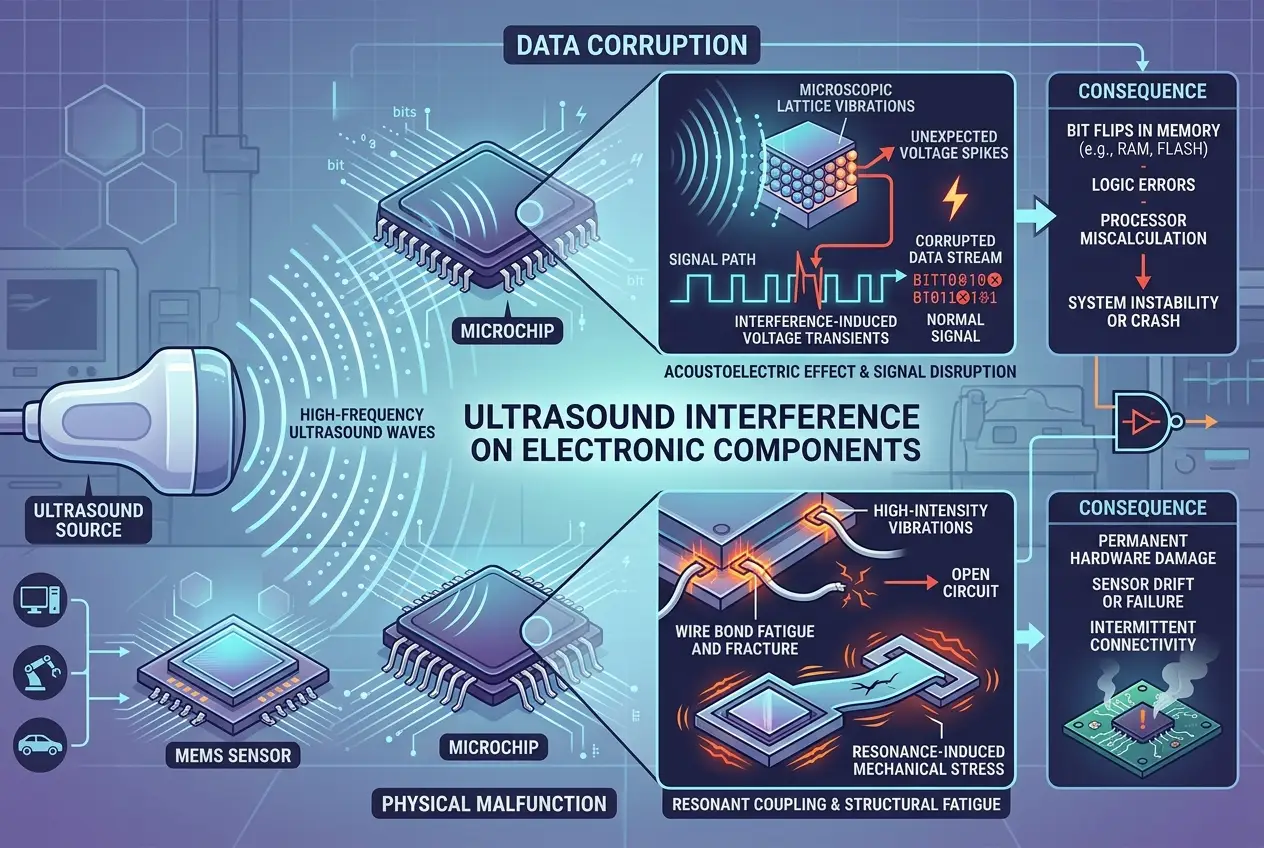
Many electronic components, especially those found in smartphones and IoT devices, rely on microscopic mechanical elements that vibrate. Accelerometers, for instance, measure acceleration by detecting changes in capacitance due to movement. Gyroscopes detect angular velocity. If you can introduce specific, powerful sound waves at resonant frequencies, you can potentially trick these sensors into reporting false data.
Imagine a drone whose accelerometer is tricked into thinking it's upside down, causing it to crash. Or a smart security camera whose gyroscope is manipulated to report constant, erratic movement, triggering false alarms or disabling its motion detection. Researchers have demonstrated that precise ultrasonic waves can inject malicious commands into MEMS (Micro-Electro-Mechanical Systems) accelerometers, effectively hijacking devices remotely. This isn't just theory; it's been proven in laboratory settings. You can read more about how MEMS sensors can be manipulated by acoustic signals on sites like Wikipedia's article on [MEMS](https://en.wikipedia.org/wiki/Micro-electromechanical_system).
Voice Assistant Hijacking
Perhaps one of the most concerning acoustic attack vectors involves voice assistants like Alexa, Google Assistant, or Siri. These devices are always listening, waiting for a wake word. What if you could embed commands into inaudible frequencies that only the device hears, but you don't?
Researchers have shown it's possible to craft ultrasonic commands that are inaudible to humans but perfectly intelligible to the microphones in smart speakers and smartphones. This allows an attacker to remotely issue commands—make calls, open malicious websites, adjust smart home settings, or even unlock doors—all without the device owner having any audible clue. The user might simply hear a slight static, if anything at all, while their device carries out instructions. This "DolphinAttack" method, as it's been dubbed, highlights a profound vulnerability in our voice-controlled world. I recall reading about similar discussions around /blogs/do-phantom-sounds-haunt-our-digital-world-4044, which explored digital anomalies, and this is a physical anomaly impacting digital systems.
Data Exfiltration via Sound
Another astonishing application of acoustic hacking is the potential for **data exfiltration**. Imagine a highly secured, air-gapped computer—one completely isolated from external networks—being breached. It sounds like science fiction, but researchers have developed methods to extract data from such systems using sound.
By subtly modulating the internal components of a computer (like fan speeds, hard drive sounds, or even coil whine from the CPU), sensitive data can be encoded into inaudible acoustic signals. A nearby microphone, perhaps in a hidden smartphone or a seemingly innocent device, could then pick up these "secret sounds" and reconstruct the data. This is a subtle and complex attack, but the very possibility challenges the notion of true air-gapped security. It makes you wonder how many unseen signals our devices might be generating, similar to how we've explored how /blogs/can-brainwaves-control-tech-from-afar-9230 could interact with technology.
As noted by cybersecurity expert Mikko Hyppönen, "There are only two types of companies: those that have been hacked, and those that don't know yet." The acoustic attack vector simply adds another layer of unknown vulnerability to this already complex landscape.
Beyond Hacking: The Broader Impact of Silent Sounds
The influence of invisible sound isn't limited to malicious hacking. These frequencies can also have unintended consequences or be leveraged for beneficial purposes.
Unintentional Interference
Powerful low-frequency infrasound can travel through buildings and materials. It's plausible that strong infrasound from industrial machinery, natural phenomena, or even poorly designed audio systems could unintentionally interfere with sensitive electronic equipment, causing glitches, performance degradation, or false readings. This could be particularly problematic for critical infrastructure or highly precise scientific instruments.
Positive Applications: The Future of Sound-Based Tech
On the flip side, the ability to manipulate devices with precise, inaudible sound also opens doors for incredible innovations. Imagine:
* **Advanced Biometrics:** Your unique ear shape or bone structure could be used to authenticate you via personalized ultrasound signals.
* **Silent Communication:** Sending data or commands between devices without disturbing humans in the vicinity.
* **Enhanced Navigation:** Using localized ultrasound beacons for highly precise indoor positioning, far more accurate than GPS.
* **Material Science:** Leveraging focused ultrasound for microscopic assembly or even self-healing materials, drawing parallels to how /blogs/can-sound-waves-forge-power-3170 discussed generating energy from sound.
Protecting Against the Unseen Threat
As acoustic hacking evolves, so too must our defenses. Here are a few ways we might mitigate these silent threats:
1. **Sensor Hardening:** Manufacturers need to design sensors that are more resilient to out-of-band frequencies. This could involve physical dampening, advanced signal filtering, or cryptographic authentication for sensor inputs.
2. **Acoustic Firewalling:** Developing software or hardware that can detect and filter out suspicious ultrasonic or infrasonic signals before they reach critical components.
3. **Environmental Awareness:** Understanding the acoustic landscape of sensitive areas and mitigating sources of powerful infrasound or ultrasound.
4. **User Education:** While we can't hear these sounds, being aware of unusual device behavior or unexplained actions is crucial. A device acting strangely might be under an acoustic attack.
The world of cybersecurity is a constant arms race, and the emergence of acoustic hacking reminds us that threats can come from unexpected places. It's a fascinating and somewhat frightening testament to the subtle power of physics and the intricate vulnerabilities inherent in our increasingly interconnected, sensor-laden world. We've built a technological ecosystem that's constantly listening, and sometimes, it's listening to things we can't even perceive. Understanding these silent signals is paramount to securing our future.
Frequently Asked Questions
It's not about being 'loud' in the audible sense, but about the energy and frequency. Electronic components like accelerometers and gyroscopes rely on tiny mechanical parts that vibrate. Infrasound and ultrasound, even if inaudible to humans, are still pressure waves that can cause these microscopic parts to vibrate at their resonant frequencies, tricking the sensor into reporting false data or causing physical interference. The energy at these specific frequencies is what matters, not perceived loudness.
Acoustic hacking methods have moved beyond theory and have been successfully demonstrated in controlled laboratory environments by researchers. Techniques like 'DolphinAttack' for voice assistant hijacking and vibration-based exploits against MEMS sensors have shown proof-of-concept. While widespread real-world attacks aren't commonly reported yet, the potential for exploitation is significant, and the research shows these are viable attack vectors.
Devices that rely heavily on microphones and micro-electromechanical systems (MEMS) sensors like accelerometers and gyroscopes are particularly vulnerable. This includes smartphones, smart speakers, smart home devices (like security cameras, thermostats), smart cars, industrial IoT sensors, and medical devices. Essentially, any device that uses sound or vibration to gather data or operate could be a target.
Currently, commercial solutions specifically marketed as 'acoustic hacking protection' are not widespread for consumer devices. However, the industry is increasingly aware of these vulnerabilities. Future devices may incorporate better physical dampening for sensors, advanced digital signal processing to filter out out-of-band frequencies, and more robust authentication protocols for sensor inputs. For critical infrastructure, specialized acoustic shielding and monitoring systems might be developed.
Yes, natural phenomena are significant sources of infrasound. While less likely to cause targeted 'hacking,' powerful infrasound generated by earthquakes, volcanic activity, severe weather, or even strong winds can potentially interfere with highly sensitive electronic equipment, especially those designed to detect subtle vibrations. This could lead to unintentional glitches, false readings, or temporary malfunctions in poorly shielded or unhardened systems.
Verified Expert
Alex Rivers
A professional researcher since age twelve, I delve into mysteries and ignite curiosity by presenting an array of compelling possibilities. I will heighten your curiosity, but by the end, you will possess profound knowledge.
Leave a Reply
Comments (0)
No approved comments yet. Be the first to share your thoughts!
Leave a Reply
Comments (0)