I recently had a moment of pure digital dread. I was sifting through an old cloud drive, cleaning out years of forgotten files, trying to achieve that satisfying feeling of a truly empty digital space. I deleted hundreds of documents, photos, and archived conversations, meticulously moving them to the trash and then hitting 'empty permanently.' Yet, a nagging thought lingered: *did they really disappear?* It’s a feeling many of us have experienced, a subtle unease that our digital past might not be as erased as we believe. This isn't just paranoia; it's a fascinating and increasingly relevant tech mystery: do deleted digital memories truly haunt our networks?
We operate under the assumption that 'delete' means 'gone.' In the physical world, tearing up a letter or shredding a document feels definitive. But in the intricate, interconnected expanse of our digital universe, true erasure is often an illusion. The very architecture of our data storage and networking systems creates a persistent shadow, a kind of digital afterlife for information we thought we had banished forever.
The Illusion of Digital Deletion
When you hit 'delete' on your computer, smartphone, or cloud service, what actually happens? It's rarely a complete, immediate obliteration of data. Instead, the operating system typically performs a much simpler operation: it removes the pointer to the file and marks the space it occupied as "available" for new data. The actual bits and bytes of your file remain on the storage medium, just waiting to be overwritten. Think of it like a library. Deleting a book doesn't burn it; it simply removes its entry from the catalog and puts it back on the shelf, hoping someone else will put a new book in its place.
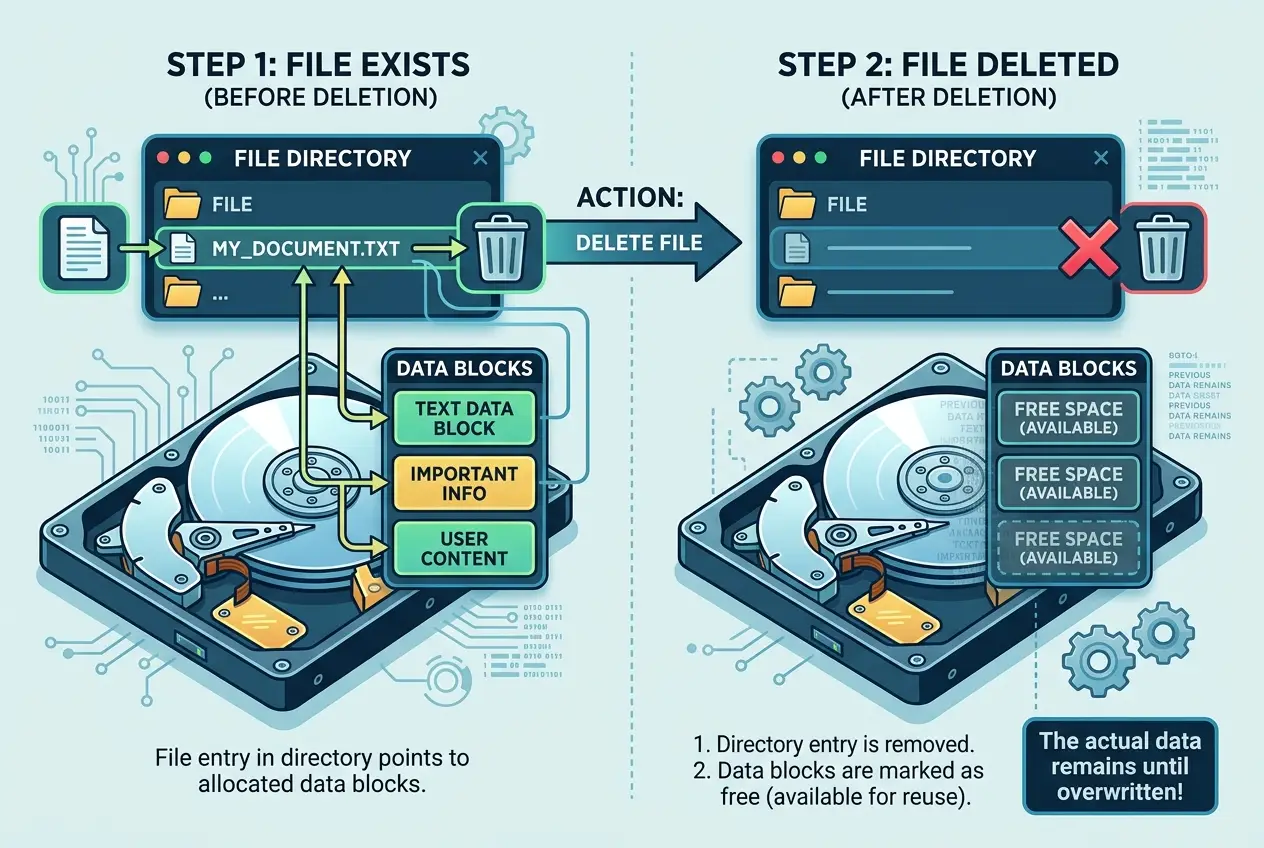
This is why data recovery software can often retrieve "deleted" files, sometimes years later, especially if the drive hasn't been heavily used since the deletion. Until new data explicitly overwrites the old, those digital remnants persist. For more on how data survives, you might find our article on
digital legacy and data survival insightful.
Beyond Your Hard Drive: The Network Effect
The plot thickens when we move beyond a single device. Our digital lives are increasingly intertwined with networks – cloud storage, email servers, social media platforms, and countless other online services. When you upload a photo to social media, send an email, or save a document to a cloud service, you're not just creating one copy; you're often creating many.
Consider this:
* **Cloud Backups:** Your phone automatically backs up to the cloud. You delete a photo from your phone. Is it deleted from the cloud backup? Maybe, maybe not, depending on the service's policies and sync settings.
* **Email Servers:** An email you sent is stored on your outbox server, the recipient's inbox server, and potentially on any intermediate servers it passed through. Deleting it from your inbox doesn't erase it from everyone else's.
* **Social Media:** Posts, photos, and messages shared on social media platforms are replicated across multiple data centers globally. Even if you "delete" a post, residual copies might exist on backup servers, content delivery networks (CDNs), or even in the caches of other users' devices.
This distributed nature of data means that a single point of deletion often doesn't guarantee universal disappearance. The internet is a vast, interconnected web where information, once released, can become remarkably resilient. You can learn more about how digital information persists even after deletion on
Wikipedia's page on Data Remanence.
Data Remanence and Digital Archaeology
The phenomenon of data remanence is the foundation of digital forensics, a field dedicated to recovering and investigating digital data for legal or investigative purposes. Digital archaeologists, as I sometimes think of them, specialize in sifting through the digital debris of computers, servers, and networks to unearth information that was thought to be gone.
In countless criminal investigations, "deleted" evidence has been crucial for solving cases. Hard drives wiped multiple times, encrypted folders, and seemingly erased messages have been painstakingly reconstructed. This isn't magic; it's the meticulous application of specialized tools and deep understanding of how data is stored and retrieved. The "ghosts" of past data are very real to law enforcement and cybersecurity experts.
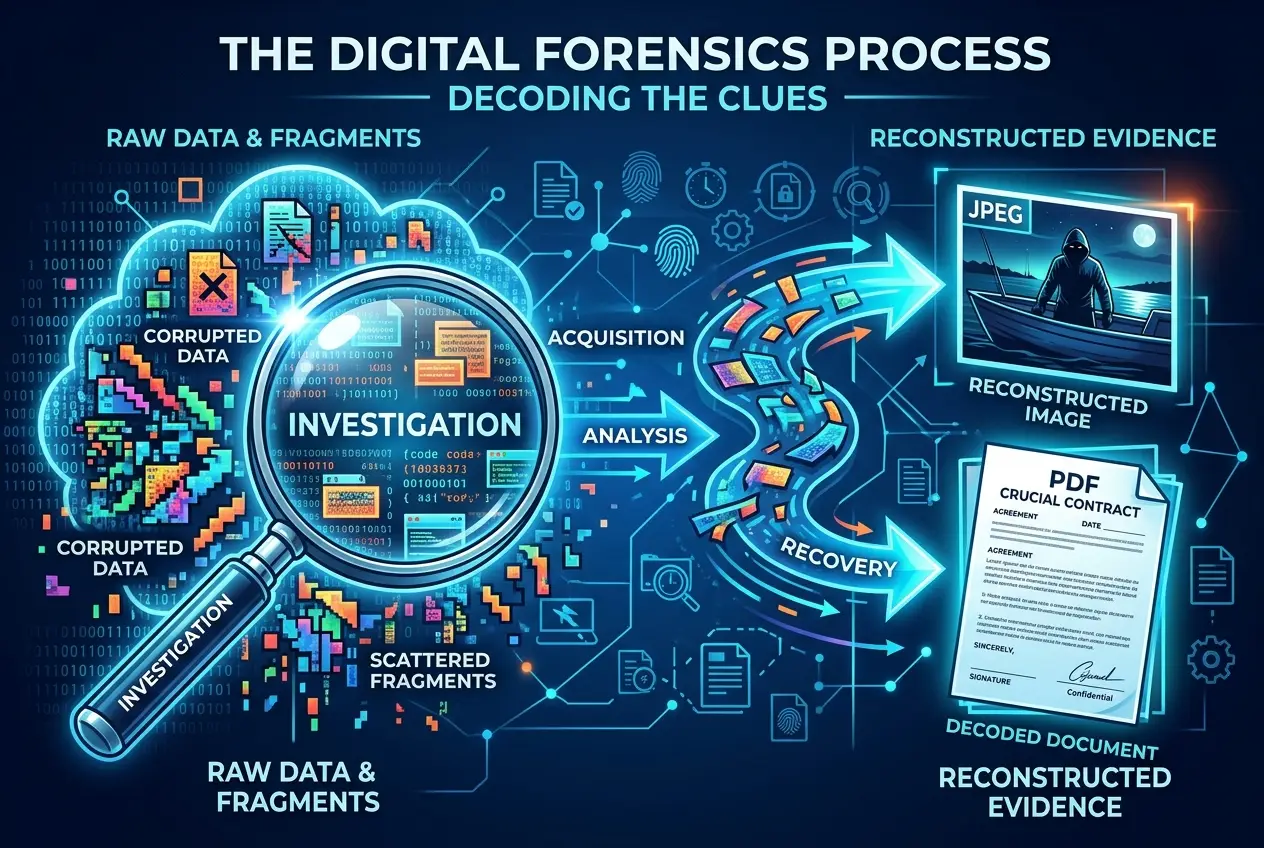
"The most persistent myth in the digital age is that of true deletion," observed a leading digital forensics expert in an interview I once read. "Every keystroke, every file, leaves a trace, a digital footprint that can be incredibly difficult to erase completely from the interconnected web of modern systems." This persistence has profound implications for our privacy.
The Ghost in the Machine: Unintended Consequences
The concept of digital ghosts isn't just theoretical; it manifests in real-world privacy concerns and unexpected resurfacings of past information. Our digital footprints are far more extensive than many of us realize, creating shadow profiles that aggregate data from various sources.
* **Privacy Breaches:** Old, supposedly deleted data residing on forgotten backup tapes or inadequately wiped servers can become a massive liability if compromised.
* **Reputational Damage:** A casual social media post from years ago, thought long gone, can resurface at an inopportune moment, impacting careers or personal lives.
* **Algorithmic Memory:** AI and machine learning algorithms are trained on vast datasets. Even if original user data is "deleted," its influence might live on in the learned patterns and predictions of these systems.
The "haunting" metaphor becomes less abstract when old data, perhaps innocuous at the time, comes back to impact individuals or organizations. It underscores the critical importance of understanding
data privacy and robust information security practices.
The Future of Deletion: Quantum and Beyond
As our digital lives become more embedded, the quest for "true" deletion gains urgency. Researchers and engineers are constantly developing new methods to achieve irreversible data destruction. These include:
* **Cryptographic Shredding:** Encrypting data with a key, then deleting *only the key*. Without the key, the data becomes unintelligible, effectively making it "gone" even if the raw bits remain.
* **Physical Destruction:** The most absolute method, involving physically shredding, degaussing (demagnetizing), or incinerating storage devices.
* **Quantum Deletion?** In the realm of quantum computing, the principles of quantum mechanics might offer novel ways to handle data. While speculative, some theoretical concepts explore how quantum states could be manipulated to ensure data is genuinely annihilated, rather than just made inaccessible. Our article on
quantum computers and time rules delves into some of these fascinating theoretical capabilities.
The challenges are immense. The sheer volume of data generated daily, combined with the distributed nature of modern computing, makes centralized, verifiable deletion incredibly difficult. This is a battle between the inherent persistence of information and our desire for control over our digital past. For more about secure information destruction,
Wikipedia has an in-depth article.
Conclusion: The Persistent Digital Shadow
The idea that deleted digital memories haunt our networks is less a spooky tale and more a profound reflection of how our digital world operates. It's a tech mystery rooted in the fundamental physics of information and the practicalities of computing infrastructure. The bits and bytes of our past, while seemingly erased, often linger in the shadows of hard drives, cloud servers, and network caches.
As we navigate an increasingly digital existence, understanding this persistence is crucial. It calls for greater digital literacy, more responsible data management practices, and a mindful approach to what we create and share online. For now, the digital ghosts remain, silent echoes of our past interactions, reminding us that in the digital realm, nothing truly vanishes without a trace.

 Join Us
Join Us































Leave a Reply
Comments (0)